Free website promotion strategies are essential for anyone looking to enhance their online presence and attract more visitors. In a digital world saturated with competition, understanding how to effectively promote your website without breaking the bank can make all the difference. This guide will delve into various approaches to elevate your site’s visibility, touching on social media, networking techniques, and video marketing.
By leveraging these methods, you can create a compelling online presence that not only reaches more users but also engages them in meaningful ways. Whether you’re a small business owner or a passionate blogger, these strategies will equip you with the tools necessary for success.
Free Website Promotion Strategies Overview
In today’s digital landscape, effectively promoting a website is crucial for enhancing online visibility and reaching potential customers. With millions of websites vying for attention, employing free promotion strategies can help businesses stand out without straining their budgets. This overview will explore various free methods to promote your website effectively and provide tips for measuring the success of these strategies.Website promotion strategies are essential for driving traffic and increasing engagement.
By utilizing free methods, businesses can tap into organic reach and build a loyal audience over time. Here are several effective free promotion strategies to consider:
Search Engine Optimization ()
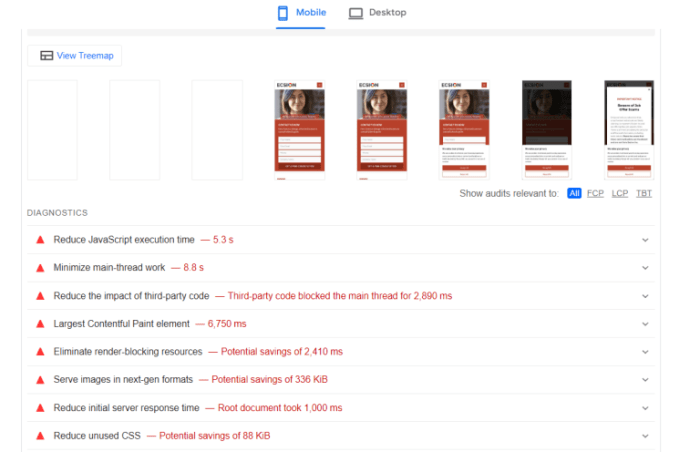
is a critical component in website promotion, aimed at improving a website’s ranking in search engine results. By optimizing content for relevant s, businesses can attract organic traffic. Key practices include:
- Conducting research to identify high-traffic terms related to your niche.
- Optimizing on-page elements such as title tags, headings, and meta descriptions.
- Creating high-quality, informative content that addresses user needs.
- Building backlinks from reputable sites to enhance authority.
The impact of can be significant, as search engines account for a large percentage of web traffic. For instance, businesses that rank in the top three positions on search engine results pages (SERPs) often experience a dramatic increase in visibility and clicks.
Social Media Engagement
Utilizing social media platforms is another effective way to promote a website for free. Engaging with audiences on platforms like Facebook, Twitter, and Instagram can drive traffic and build community. Here’s how to leverage social media:
- Sharing valuable content that resonates with your audience.
- Participating in conversations and responding to comments and messages.
- Using relevant hashtags to expand the reach of your posts.
- Collaborating with influencers or other brands to tap into their audiences.
Social media allows for real-time interaction, fostering a sense of connection with followers. This engagement can lead to increased brand loyalty and referrals, as satisfied customers are likely to share their positive experiences.
Content Marketing
Content marketing focuses on creating and distributing valuable content to attract and engage a target audience. This strategy can enhance brand awareness and drive traffic. Here are several approaches to effective content marketing:
- Writing blog posts that provide solutions to common problems faced by your target audience.
- Creating informative infographics that visually represent useful data.
- Producing videos that can be shared across various platforms.
- Offering free resources or tools that provide value, such as eBooks or guides.
High-quality content can position a business as an authority in its industry, encouraging visitors to return for more information and share it with others.
Email Marketing
Email marketing remains a powerful tool for promoting a website, allowing businesses to communicate directly with their audience. Free email marketing tools can help start this process effectively. Key strategies include:
- Building an email list by offering incentives for sign-ups, like exclusive content or discounts.
- Sending regular newsletters with updates, promotions, and valuable content.
- Personalizing emails to cater to individual recipient preferences.
- Encouraging subscribers to share emails with friends and family to expand reach.
Email marketing can lead to higher conversion rates, as targeted messages are more likely to resonate with recipients.
Measuring the Success of Promotional Strategies
Measuring the effectiveness of free promotional strategies is essential for understanding what works. Here are several key performance indicators (KPIs) to consider:
- Website traffic: Use tools like Google Analytics to track the number of visitors and their behavior on the site.
- Conversion rate: Measure how many visitors take desired actions, such as signing up for a newsletter or making a purchase.
- Engagement metrics: Monitor social media interactions, including likes, shares, and comments.
- Search engine rankings: Regularly check rankings to assess effectiveness.
By analyzing these metrics, businesses can refine their promotional strategies over time, ensuring continued growth and engagement.
Social Media and Networking Techniques

To effectively promote your website, leveraging social media and networking techniques is crucial. Social media platforms provide a vast audience and an opportunity to engage with potential visitors directly. By employing strategic networking, you can enhance your website’s visibility and attract more traffic.Social media is a powerful tool for website promotion, allowing for real-time engagement and sharing. This section explains how to utilize various platforms effectively and Artikels networking strategies to boost traffic.
Leveraging Social Media Platforms
Social media platforms like Facebook, Twitter, Instagram, and LinkedIn can significantly amplify your online presence. Here are effective strategies for promoting your website through these channels:
- Create Shareable Content: Craft engaging and valuable content that encourages users to share it with their networks, increasing organic reach.
- Utilize Visuals: Posts with images or videos tend to generate higher engagement. Infographics or short videos summarizing your content can be particularly effective.
- Engage with Followers: Respond to comments and messages promptly. Building a community around your brand can lead to loyal visitors who actively promote your website.
- Run Contests or Giveaways: Incentivizing shares and interactions through contests can rapidly increase your audience and drive traffic to your site.
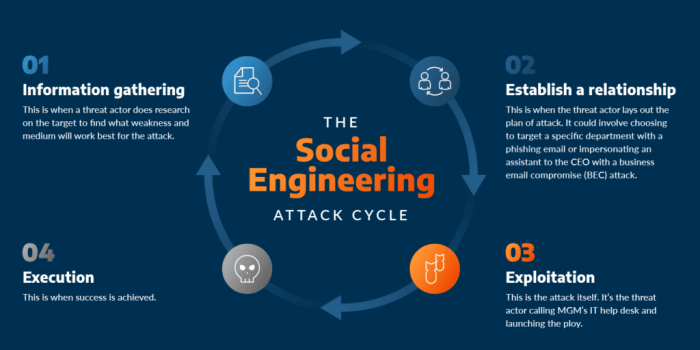
Effective Social Networking Strategies
Networking can create valuable connections that lead to website promotion. Here are some strategies that can increase traffic through social networking:
- Join Relevant Groups: Participate in groups related to your niche on platforms like Facebook or LinkedIn. Share insights and link back to your website when appropriate.
- Collaborate with Influencers: Partnering with influencers in your industry can expose your website to their followers, driving traffic and building credibility.
- Attend Virtual Events: Webinars and online conferences provide opportunities to network and share your website with like-minded individuals.
- Engage in Industry Discussions: Commenting on relevant posts or articles can establish your authority and encourage others to check out your website.
The Role of Social Bookmarking
Social bookmarking can play a significant role in expanding your website’s reach. By submitting your website links to social bookmarking sites, you can enhance visibility and encourage more visits. The following points highlight its importance:
- Increased Visibility: Bookmarking your website on platforms like Reddit or Digg can attract users looking for new content.
- Traffic Generation: When users discover and click on your links, it can lead to a surge in traffic and improve your site’s ranking.
- Community Engagement: Engaging with users who bookmark your content provides an opportunity to interact and foster a loyal audience.
“Utilizing social media and networking effectively can transform your website’s reach and engagement, turning casual visitors into loyal followers.”
Video Marketing and Streaming
Video marketing is a powerful tool for boosting website engagement and attracting new visitors. As online consumption of video content continues to rise, integrating video into your marketing strategy can significantly enhance the user experience on your website. This guide explores how to leverage video marketing effectively, the best platforms for video streaming, and techniques to improve through video integration.
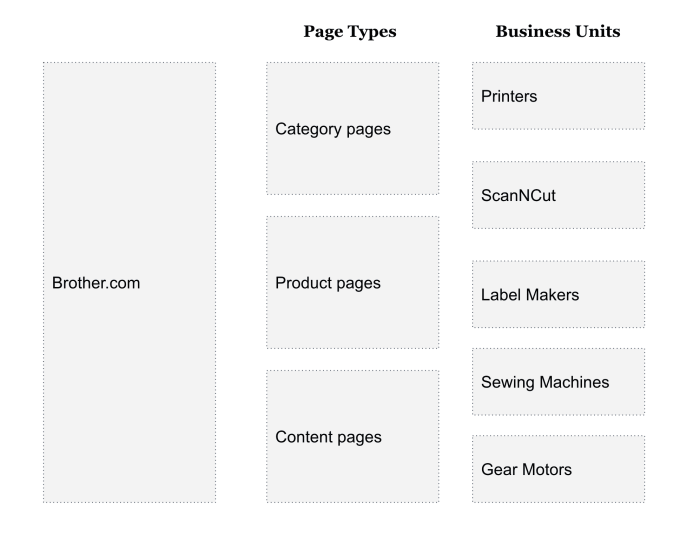
Guide on Using Video Marketing to Boost Website Engagement
Utilizing video marketing can increase the visibility and engagement of your website. Videos can convey complex information quickly and effectively, appealing to a broad audience. Here are some strategies to enhance your website engagement using video marketing:
- Create Engaging Content: Focus on producing high-quality videos that are entertaining, informative, or both. Content such as tutorials, behind-the-scenes looks, and customer testimonials can resonate well with viewers.
- Use Call-to-Action: Always include a clear call-to-action (CTA) at the end of your videos. This could be directing viewers to subscribe, visit your website, or engage with other content.
- Optimize Video Length: Keep your videos concise. Research suggests that videos under two minutes hold viewers’ attention better, making them more likely to engage with your content.
- Promote Video Content: Share your videos across various platforms such as social media, email newsletters, and on your website to expand reach and drive traffic.
Platforms for Video Streaming that Can Promote a Website
Selecting the right platforms for video streaming is crucial to maximizing your reach and engagement. Here are some popular platforms that can help promote your website effectively:
- YouTube: As the largest video-sharing platform, YouTube allows you to reach a massive audience. By optimizing your video titles, descriptions, and tags, you can enhance discoverability and drive traffic to your website.
- Vimeo: Known for its professional quality, Vimeo is ideal for businesses looking to showcase high-quality video content. It also allows for customizable video players that can be embedded directly on your website.
- Facebook Live: Live streaming on Facebook promotes real-time engagement with your audience, allowing you to answer questions and drive immediate traffic to your website.
- Instagram Reels: Short, snappy videos on Instagram can capture attention quickly. Use them to promote products or share valuable tips that link back to your website.
Techniques for Integrating Videos into Website Content for Better Results
Integrating videos into your website doesn’t just enhance user experience; it can also significantly improve your ranking. Here are effective techniques for optimizing video content for :
- Optimize Video Metadata: Ensure video titles, descriptions, and tags are -rich and relevant to the content. This helps search engines understand the context of the video.
- Provide Transcriptions: Including a text transcription of your video content can enhance accessibility and allow search engines to index your video’s content, improving discoverability.
- Embed Videos on Relevant Pages: Position your videos on pages where they provide value, such as product pages or blog posts. This can increase the time visitors spend on your site, which positively influences .
- Use Schema Markup: Implementing schema markup for video content helps search engines understand your video content better and can enhance visibility in search results.
“Incorporating video into your web strategy can lead to a 157% increase in organic traffic from search engines.”
Final Thoughts

In summary, mastering free website promotion strategies can significantly impact your online visibility and audience engagement. By implementing the techniques discussed, such as utilizing social media effectively and incorporating video marketing, you can create a dynamic and interactive online presence. Remember, consistency and creativity are key in this digital landscape, so keep experimenting with different strategies to find what works best for you.
Question & Answer Hub
What are some effective free promotion methods?
Using social media, engaging in online communities, and creating shareable content are all effective free methods.
How can I measure the success of my promotional strategies?
Utilize analytics tools such as Google Analytics to track website traffic, engagement rates, and conversion metrics.
Is video marketing necessary for website promotion?
While not strictly necessary, video marketing can greatly enhance user engagement and improve your website’s .
Can social bookmarking help my website?
Yes, social bookmarking can increase your website’s reach and drive traffic by allowing users to share content easily.
How often should I promote my website on social media?
Consistency is key; aim to post regularly without overwhelming your audience, typically a few times a week works well.